The stunning reality is that the majority of retailers accepting credit cards are still vulnerable to the newest threat to accepting credit cards from consumers. Lazarus Alliance has been years ahead with proactive cybersecurity services.
Researchers from the Cisco Security Solutions team have dubbed the latest malware to attack point-of-sales (POS) systems PoSeidon. Compromised POS systems are vulnerable to these attacks, which allow the RAM of an infected terminal to be scanned by the malware. PoSeidon looks for unencrypted credit card data and then transmits that data out to an exfiltration server controlled by the cyber criminals.
This technique has long been known to security experts. The Proactive Cybersecurity™ services at Lazarus Alliance have been years ahead of this issue by offering solutions to companies that utilize POS systems that ensure this memory scraping technique does not compromise a payment process.
William Ochs, GRC Partner of Lazarus Alliance, said, “Not only has Lazarus Alliance long called for end-to-end encryption technology to be utilized to mitigate the risk posed by POS threats, but Lazarus Alliance also has a proven track record of offering actual solutions to implement end-to-end encryption protecting retailers globally.”
As long as organizations remain reactive instead of proactive in their approach to cybersecurity, they will continue to fail the constituents they work to protect. The PoSeidon POS malware program is another example in a daunting list of the challenges that face organizations concerned with their PCI DSS stance.
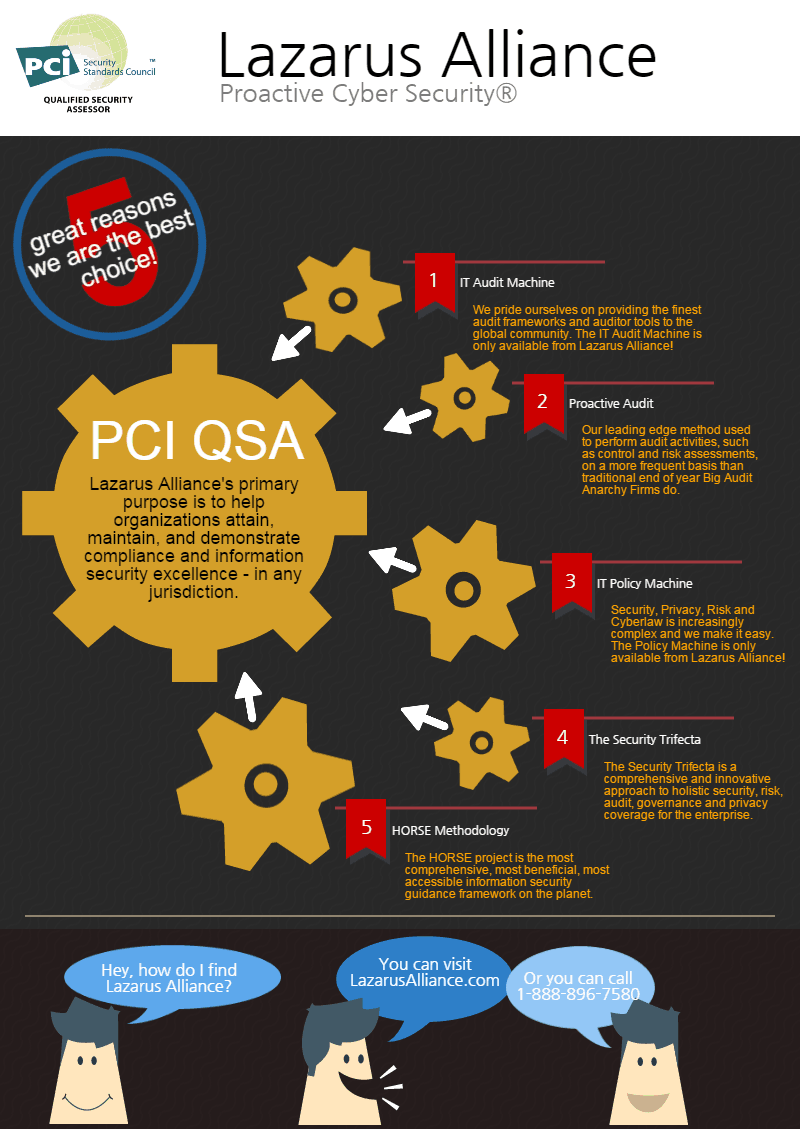
As a PCI DSS audit Qualified Security Assessor (QSA) company, Lazarus Alliance has been approved by the PCI Security Standards Council (SSC) to measure an organization’s compliance to the PCI DSS audit standard. Lazarus Alliance specializes in providing our clients with scalable, efficient solutions for meeting the rigorous demands of Payment Card Industry (PCI) compliance. We do this in part because of our breakthrough proprietary technologies called the IT Audit Machine (ITAM) and the Policy Machine.
“It’s incumbent upon security professionals to proactively advocate for best practices in cybersecurity, risk, and compliance; too often, the opposite occurs in the industry,” said Ochs
Learn more about Lazarus Alliance and why Lazarus Alliance is Proactive Cybersecurity™!