Lazarus Alliance: Proactive NIST CSF & 800-53 Audit Services. Call +1 (888) 896-7580 today!


Lazarus Alliance’s pre-assessment process provides organizations with a targeted, efficient review of their NIST CSF 2.0 program by directly examining the underlying NIST SP 800-53 control implementations through rigorous validation testing. As an A2LA-accredited laboratory and certified 3PAO, Lazarus Alliance leverages its Security Control Assessment & Validation (SCA-V) services and proprietary Continuum GRC IT Audit Machine™ (ITAM) platform to bridge the high-level, outcome-based CSF (106 Subcategories) with the detailed, prescriptive controls in NIST 800-53 Rev. 5.
NIST CSF organizes its Core into 6 high-level Functions and 22 Categories (the Categories sit under the Functions and contain the 106 Subcategories).
Lazarus Alliance, a certified Third-Party Assessment Organization (3PAO), will collaborate directly with your organization to schedule your NIST CSF & 800-53 assessment. Our certified 3PAO assessors will assist in determining the appropriate impact level based on your company’s unique business and government requirements.
The following matrix represents the required functions to achieve CSF compliance.
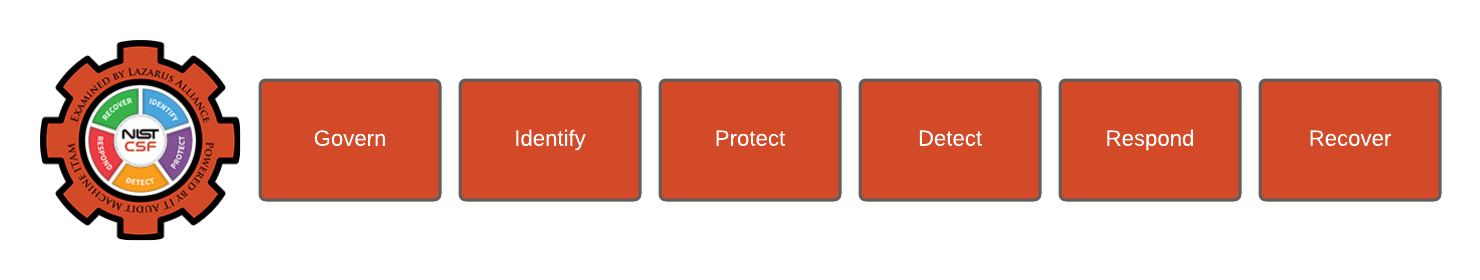
- Govern (GV): The organization’s cybersecurity risk management strategy, expectations, and policy are established, communicated, and monitored.
- Identify (ID): The organization’s current cybersecurity risks are understood.
- Protect (PR): Safeguards to manage the organization’s cybersecurity risks are used.
- Detect (DE): Possible cybersecurity attacks and compromises are found and analyzed.
- Respond (RS): Actions regarding a detected cybersecurity incident are taken.
- Recover (RC): Assets and operations affected by a cybersecurity incident are restored.
The following matrix represents the required functions to achieve 800-53 compliance.
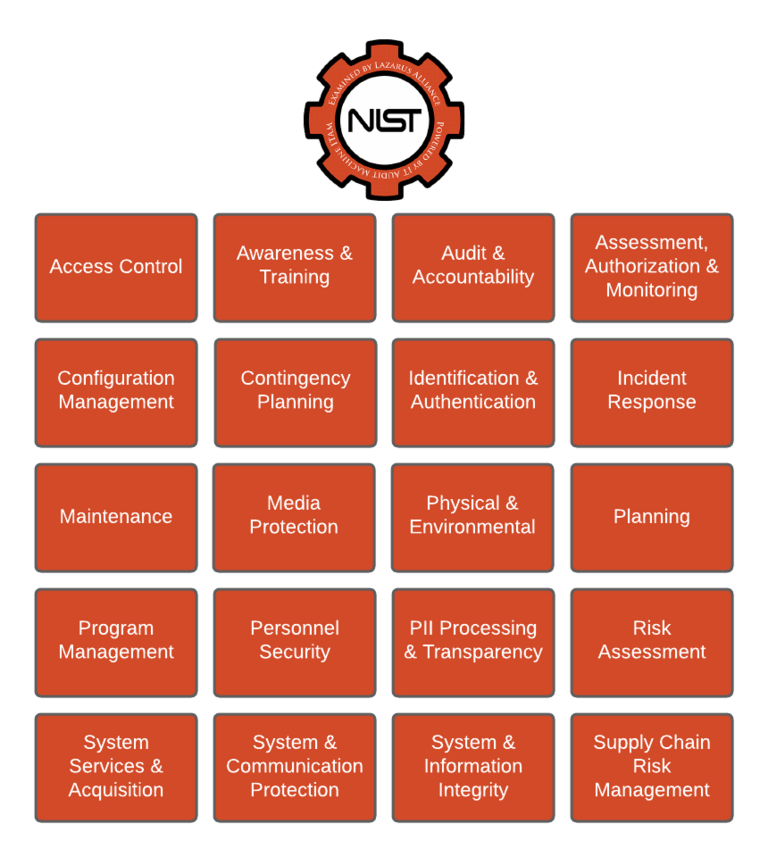
A System is holistically comprised of the Technology, People, Processes, and Data used to complete the services provided. The 800-53 certification is designed to provide comfort over the following principles described in brief:
- Access Control: This control environment measures the security features of the system boundary that control access rights and resources. Areas to be examined include, but are not limited to: account management, access enforcement, unsuccessful login attempts, system use notification, permitted actions, permitted actions without identification/authorization, remote access, wireless access, access control for mobile devices, use of external information systems, and publicly accessible content.
- Awareness and Training: This control environment measures the security awareness training that the organization has in place, with respect to the system boundary. Areas to be examined include, but are not limited to: security awareness, security training, and security training records.
- Audit and Accountability: This control environment measures the resources in place to measure and hold accountable audit practices over the system boundary. Areas to be examined include, but are not limited to: audit events, content of audit records, audit storage and capacity, response to audit processing failures, audit review process, time stamps, and protection of audit information, audit record retention, and audit generation.
- Assessment Authorization and Monitoring: This control environment examines how organizations assess controls in systems and the environments in which those systems operate as part of initial and ongoing authorizations, continuous monitoring, FISMA annual assessments, system design and development, systems security engineering, privacy engineering, and the system development life cycle.
- Configuration Management: This control environment examines the configurations around the system boundary. Areas to be examined include, but are not limited to: baseline configurations, security impact analysis, configuration settings, least functionality, information system component inventory, software usage restrictions, and user-installed software.
- Contingency Planning: This control environment examines the organization's processes around contingencies. Areas to be examined include, but are not limited to: the contingency plan, contingency training, plan testing, information system backup, and information system recovery and reconstitution.
- Identification and Authentication: This control area examines the procedures and tools in place to identify and authenticate users who are granted access to the system boundary. Areas to be examined include, but are not limited to: identification and authentication, identifier management, authenticator management, authenticator feedback, and cryptographic module authentication.
- Incident Response: This control area examines the process and practices in place for handling and responding to incidents within the system boundary. Areas to be examined include, but are not limited to: incident response training, handling, monitoring, reporting, response assistance, and the incident response plan.
- Maintenance: This control area examines the processes and procedures in place that support controlled maintenance within the system boundary. Areas to be examined include, but are not limited to: controlled maintenance, nonlocal maintenance, and maintenance personnel.
- Media Protection: This control area examines the processes and procedures in place that support proper protections around system media assets. Areas to be examined include, but are not limited to: media access, sanitization, and disposal.
- Physical and Environmental: This control area examines the process and procedures in place, which support proper physical and environmental protections to the system boundary. Areas to be examined include, but are not limited to: physical access control and authorizations, monitoring physical access, visitor access records, emergency lighting, fire protection, temperature and humidity controls, water damage protection, and delivery and removal.
- Planning: This control area examines the processes in place around proper planning for the system boundary. Areas to be examined include, but are not limited to: The System Security Plan and rules of behavior.
- Program Management: This control environment measures the organization’s status in the development and implementation of an organization-wide information security program to address information security for the information and information systems that support the operations and assets of the organization, including those provided or managed by another organization, contractor, or other source.
- Personnel Security: This control environment measures the practices and processes in place that examine, screen, and review personnel assigned to the system boundary. Areas to be examined include, but are not limited to: position risk designation; personnel screening, termination, and transfer; access agreements, third-party personnel, and personnel sanctions.
- Personally Identifiable Information Processing and Transparency: This control environment measures the Personally Identifiable Information; Any representation of information that permits the identity of an individual to whom the information applies to be reasonably inferred by either direct or indirect means.
- Risk Assessment: This control area examines the process and procedures in place, which measure risk and vulnerabilities to the system boundary. Areas to be examined include, but are not limited to: security categorization, risk assessment, and vulnerability scanning.
- System Services and Acquisition: This control environment measures the practices and processes in place for the development of the system boundary. Areas to be examined include, but are not limited to: allocation of resources, the system development life cycle, acquisition process, information system documentation, and external information system services.
- System and Communication Protection: This control area examines the process and procedures in place, which measure the protection of the system boundary. Areas to be examined include, but are not limited to, denial of service protection, boundary protection, cryptographic key establishment, protection and management, collaborative computing devices, secure name/address resolution devices, provisioning architecture, and process isolation.
- System and Information Integrity: This control environment measures the practices and processes in place for the assurance of system boundary integrity. Areas to be examined include, but are not limited to: flaw remediation, malicious code protection, information system monitoring, and information handling and retention.
- Supply Chain Risk Management: This control environment measures the practices and processes in place for identifying, assessing, and mitigating ICT supply chain risks at all levels of their organizations.
Lazarus Alliance 800-53 client services will schedule our team to prioritize this engagement based on the needs of the client and ensure a timely delivery of the required compliance package, subject to client resources being available.
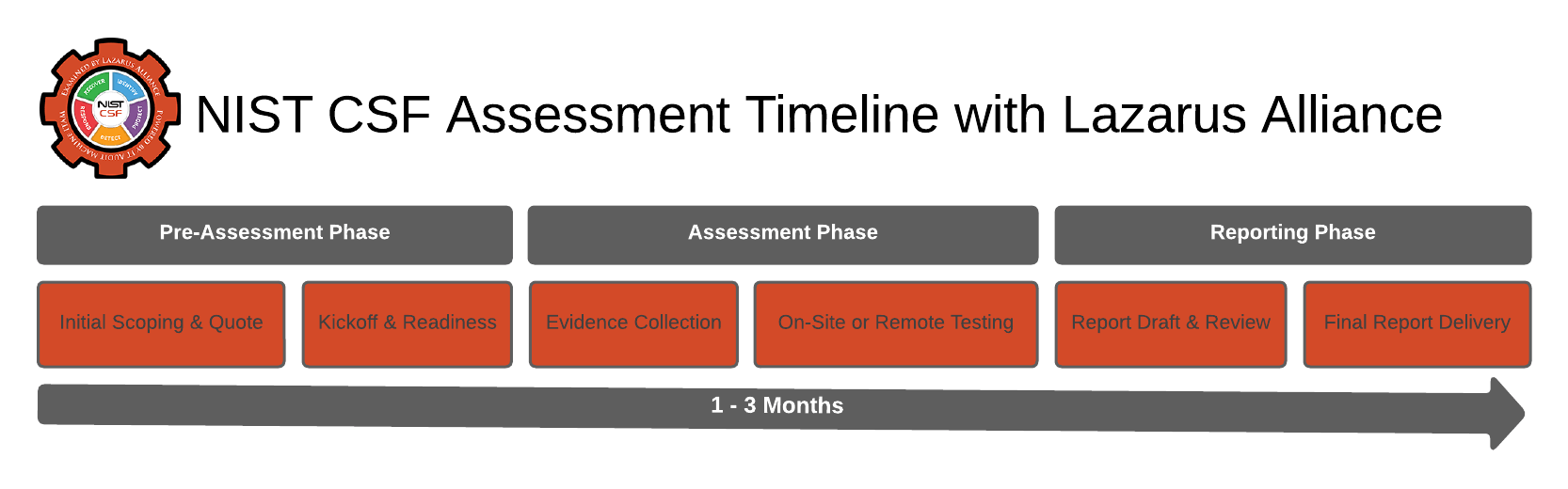
Audit Timeline: What to Expect with Lazarus Alliance
Lazarus Alliance’s combined NIST CSF 2.0 + NIST SP 800-53 assessment uses our SCA-V (Security Control Assessment & Validation) service. We validate your CSF program outcomes by rigorously testing the underlying NIST 800-53 Rev. 5 controls (via official Informative References mappings and NIST SP 800-53A assessment procedures).
Typical Timeline (from Kickoff to Final SAR)
6–12 weeks total — accelerated by 46% compared to traditional manual audits thanks to their proprietary Continuum GRC IT Audit Machine™ (ITAM) platform, Critical Path Methodology, and Cybervisor™ advisory support.
- Fastest realistic timeline (well-prepared client with pre-loaded evidence and full automation): ~6–8 weeks
- Average timeline (most organizations): 8–10 weeks (includes minor remediation)
- Longest common timeline: 10–12+ weeks (complex scopes, large environments, or extensive POA&Ms)
Detailed NIST Cybersecurity Framework (CSF) & NIST SP 800-53 Audit & Compliance Timeline
Lazarus Alliance follows this structured 6-phase process for NIST CSF + 800-53 (moderate/high baseline) audits, gap assessments, and continuous authorization support.
| Phase | Activities | Typical Duration | Key Deliverables & Tools |
|---|---|---|---|
| Phase 0 – Pre-Engagement & Decision | Initial consultation, scope definition, NDA, and engagement letter | 1–2 weeks | Signed SOW, project charter, and Continuum GRC portal access |
| Phase 1 – Kickoff & Scoping | Kickoff meeting, CSF core function mapping (Identify, Protect, Detect, Respond, Recover), 800-53 control baseline selection | Week 0–1 | Finalized NIST CSF + 800-53 scope document, tailored control list, document request list |
| Phase 2 – Gap Assessment & Evidence Collection | Current-state assessment, gap analysis against CSF and 800-53 controls, evidence upload | Weeks 1–5 | Complete evidence package in Continuum GRC, detailed gap remediation plan |
| Phase 3 – Remediation & Validation | Remediation support, control implementation, policy updates, and configuration hardening | Weeks 5–9 | Validated controls, updated SOPs, and training records |
| Phase 4 – Assessment Fieldwork & Testing | Control testing, interviews, vulnerability assessments, penetration testing, mock audits | Weeks 9–12 | Testing results, preliminary findings report, and real-time dashboards |
| Phase 5 – Reporting, Certification & Ongoing Maintenance | Final report delivery, findings resolution, continuous monitoring plan, and annual assessment planning | Weeks 12–14 + ongoing | Final NIST CSF + 800-53 compliance report, attestation package, Cybervisor™ continuous monitoring roadmap |
Why clients finish faster with Lazarus Alliance: Our Proactive Cyber Security® methodology, Cybervisor™ platform, and Continuum GRC automation typically reduce NIST CSF + 800-53 assessment time by 40–50% while delivering higher-quality, defensible documentation and continuous compliance.
Pro Tip from Lazarus Alliance: Start with a free Cybervisor™ consultation and upload evidence 2–4 weeks before kickoff to hit the 6–8 week fast track. Ongoing continuous monitoring via ITAM keeps future reassessments even shorter.
If your environment is especially complex or you want a customized quote/timeline based on your scope, reach out for a no-obligation scoping call. We can often compress it further with our Continuum GRC automation.
Frequently Asked Questions
NIST CSF 2.0 is the latest voluntary Cybersecurity Framework from the National Institute of Standards and Technology. Released in February 2024, it provides a flexible, outcome-based approach with 6 Functions, 22 Categories, and 106 Subcategories to help any organization manage cybersecurity risk. Unlike version 1.1, it adds a new “Govern” function for strategic oversight and emphasizes supply-chain risk. NIST CSF 2.0 has 106 Subcategories (high-level outcomes), while the NIST 800-53 Moderate baseline has 287 controls (including enhancements). CSF is not a control catalog — it’s an outcome framework that maps directly to 800-53 controls via official Informative References. NIST provides official Informative References (via the OLIR program and CPRT tool) that link every CSF Subcategory to specific 800-53 controls. One CSF outcome can map to multiple 800-53 controls, and vice versa. This makes the two frameworks highly complementary: CSF for strategy and 800-53 for detailed, auditable implementation. A typical Lazarus Alliance combined NIST CSF 2.0 + NIST 800-53 assessment takes 6–12 weeks, with well-prepared clients completing it in 6–8 weeks. Their proprietary IT Audit Machine™ (ITAM) and Security Trifecta methodology accelerate the process by up to 46% compared to traditional audits. Lazarus Alliance’s accredited SCA-V service includes scoping, evidence collection via ITAM, automated + manual testing (scans, interviews, penetration testing), findings adjudication, a full Security Assessment Report (SAR), and optional remediation validation. As an A2LA-accredited 3PAO, they deliver defensible results for FISMA, RMF, or commercial compliance. Lazarus Alliance is an A2LA-accredited 3PAO with proprietary automation (ITAM) and Cybervisor™ advisory teams that deliver faster, more accurate assessments. They seamlessly bridge CSF outcomes with 800-53 controls, provide continuous monitoring, and have helped organizations achieve ATOs and FedRAMP authorization with 46% time savings. NIST CSF 2.0 is voluntary for all organizations but is widely adopted as the de facto standard for cybersecurity risk management. Many regulators, customers, and insurers reference it, making it essential for demonstrating due diligence even when not strictly required by law. Start with a free Cybervisor™ consultation, gather your SSP, policies, and artifacts, and upload them early to the ITAM platform. Focus on mapping your current CSF Profile to 800-53 controls and addressing any gaps identified in the pre-assessment. Lazarus Alliance provides full support from planning through authorization and continuous monitoring.
What is NIST CSF 2.0?
How many controls are in NIST CSF 2.0 vs NIST 800-53 Moderate baseline?
How does NIST CSF 2.0 map to NIST SP 800-53 in 2026?
How long does a NIST CSF + 800-53 assessment take with Lazarus Alliance?
What does a Lazarus Alliance NIST 800-53 audit include?
Why choose Lazarus Alliance for NIST CSF and 800-53 compliance?
Is NIST CSF mandatory or just recommended?
How can organizations prepare for a successful NIST CSF + 800-53 assessment with Lazarus Alliance?

Benefits of NIST CSF & NIST 800-53 Compliance
A combined NIST CSF 2.0 + NIST SP 800-53 audit (often delivered as Lazarus Alliance’s SCA-V service) delivers far more than a simple compliance checkbox. It validates that your high-level CSF outcomes are backed by real, tested 800-53 controls — producing measurable improvements in security, efficiency, and business value.
Here are the top benefits organizations consistently realize:
- Stronger Cybersecurity Posture & Resilience: You move from reactive “check-the-box” security to proactive, outcome-based protection. The audit identifies gaps in the 6 CSF Functions and 22 Categories, then confirms they are addressed by effective 800-53 controls (e.g., access control, incident response, continuous monitoring), reducing breach likelihood and impact.
- Better Risk Management & Prioritization: CSF’s risk-based Profiles + 800-53’s detailed controls give you a clear Current vs. Target view. You can prioritize high-impact risks, tailor controls to your specific environment (Low/Moderate/High baseline), and integrate cybersecurity into enterprise risk management.
- Regulatory & Contractual Compliance (FISMA, FedRAMP, RMF, etc.): The audit produces defensible evidence for Authorization to Operate (ATO), FedRAMP, DoD RMF, and other mandates. It also maps easily to HIPAA, CMMC, ISO 27001, SOC 2, and more — often satisfying multiple frameworks in a single effort.
- Competitive Advantage & Stakeholder Trust: Customers, partners, insurers, and regulators see documented proof of mature cybersecurity. Many federal and commercial contracts now require or prefer NIST-aligned programs, giving you an edge in bids and negotiations.
- Operational Efficiency & Cost Savings: Automated evidence collection, gap analysis, and continuous monitoring reduce manual work. Organizations typically see 30–46% faster assessments and lower long-term compliance costs by eliminating redundant controls and duplicate audits.
- Governance, Oversight & Continuous Improvement: The new “Govern” function in CSF 2.0 ensures executive-level accountability. You receive a Security Assessment Report (SAR), POA&M, and maturity scoring that feed directly into ongoing improvement — turning one-time audits into a living cybersecurity program.
- Faster, Smarter Results with Lazarus Alliance: As an A2LA-accredited 3PAO, Lazarus Alliance uses the IT Audit Machine™ (ITAM) platform and Security Trifecta methodology to deliver the entire CSF + 800-53 assessment in 6–12 weeks (often 6–8 weeks for prepared clients). You also get 24/7 portal access, proactive continuous monitoring, and optional remediation validation — all at a fraction of the time and cost of traditional manual audits.
In short, the audit doesn’t just prove compliance — it builds a more secure, agile, and trustworthy organization while saving time and money.
Many clients start with a free Cybervisor™ consultation and pre-assessment to see exactly where their gaps are before committing to the full audit.

Talk with one of our experts
Our Lazarus Alliance Cybervisor™ teams have experience performing thousands of assessments for organizations providing services to clients around the world.
We're here to answer any questions you may have.

Credentials You Can Count On

American Association for Laboratory Accreditation (A2LA) ISO/IEC 17020 accredited certification number 3822.01.
Lazarus Alliance utilizes the Continuum GRC IT Audit Machine, Security Trifecta methodology, and Policy Machine to deliver internationally recognized “Best Practices” for establishing organizational security standards and controls. These support compliance with NIST CSF & NIST 800-53-based audit certifications and assessments.