IT Pre-Acquisition Assessment Services | M&A Cybersecurity Due Diligence - Lazarus Alliance. Call +1 (888) 896-7580 today!
The Lazarus Alliance IT Pre-Acquisition Assessment is a structured, phased cybersecurity and IT due diligence program designed for any organization undergoing mergers, acquisitions, divestitures, or private-equity transactions. It rapidly identifies material IT, cybersecurity, data protection, and regulatory risks while minimizing disruption to the target company’s operations.
Using our proprietary two-wave Client Request List (CRL) and Continuum GRC platform, the assessment delivers actionable intelligence in 4–8 weeks, giving acquirers the clarity they need to protect deal value and ensure a smooth post-close transition.
Core Characteristics of the Audit
-
Scope: 8 sections covering the full IT and security environment, plus acquisition-specific transition risks:
- IT Governance and Asset Inventory (MSP ownership, hardware/software inventories, policies, BC/DR plan)
- Identity and Access Management (user accounts, MFA, admin privileges, password policies)
- Endpoint and Network Security (EDR/AV, patching, firewalls, network diagrams, vulnerability scanning)
- Data Protection and Confidentiality (backups, encryption, client portals, data storage/flows)
- Cloud and SaaS Environment (Microsoft 365 Secure Score, DLP, external sharing, AI tools, SOC 2 reports)
- FTC Safeguards Rule Compliance (GLBA) (Written Information Security Program / WISP, Qualified Individual designation, risk assessments, training, vendor agreements). While Section F includes the FTC Safeguards Rule (GLBA) as a common example, the framework is fully customizable to any industry’s regulatory environment (HIPAA, PCI DSS, ISO 27001, CMMC, etc.)
- Cyber Incident History and Threat Exposure (incident summary, cyber insurance certificate, phishing tests, external attack surface)
- Transition-Specific Information (system inventories, contract termination/assignment terms, data preservation, departing staff)
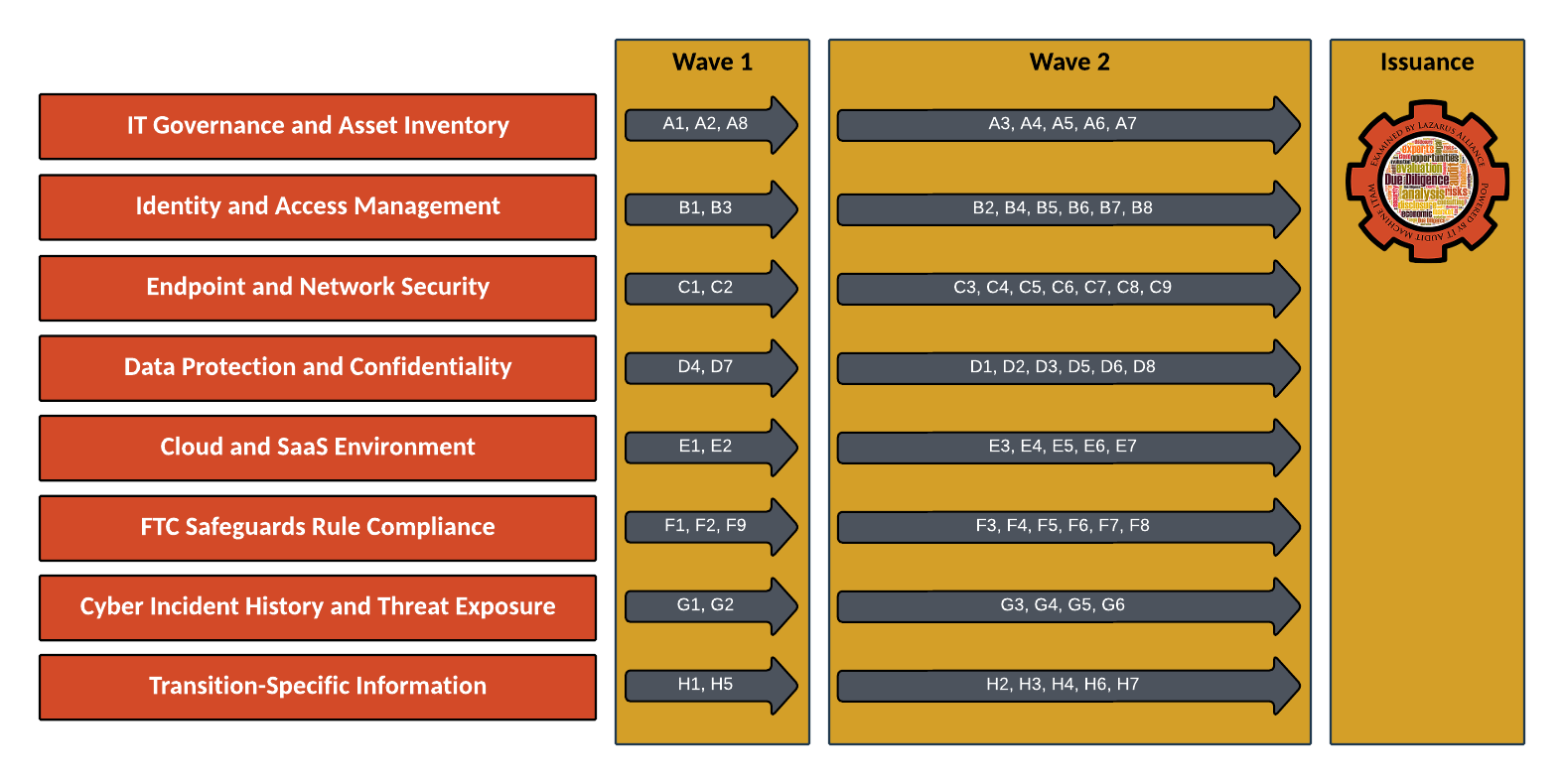
- Phased “Wave” Structure (to respect a smaller firm’s capacity):
- Wave 1 (≈18–20 items, “Issue Immediately”): Highest-risk, quick-to-obtain items that determine whether deeper investigation is warranted. Covers MSP contract, active user accounts, MFA enforcement, EDR coverage, patch status, backups, M365 config/Secure Score, WISP/QI designation, cyber insurance, incident history summary, and basic transition inventory.
- Wave 2 (≈42–44 items, “Issue After Wave 1 Review”): More labor-intensive items (detailed policies, vulnerability scans, data-flow maps, admin rights reviews, SOC 2 reports, etc.). Issued only after Wave 1 is substantially complete and reviewed; scope may be narrowed or expanded based on findings.
- Submission Rules:
- All uploads go into pre-defined section folders in the Continuum GRC portal.
- Acceptable formats are explicitly listed (Excel/CSV exports, screenshots, PDFs, Word docs, or brief written confirmations).
- If a document does not exist, upload a short written confirmation — absence is noted as a finding but not penalized.
- MSP coordination is strongly recommended (many Wave 1 exports come directly from the MSP console).
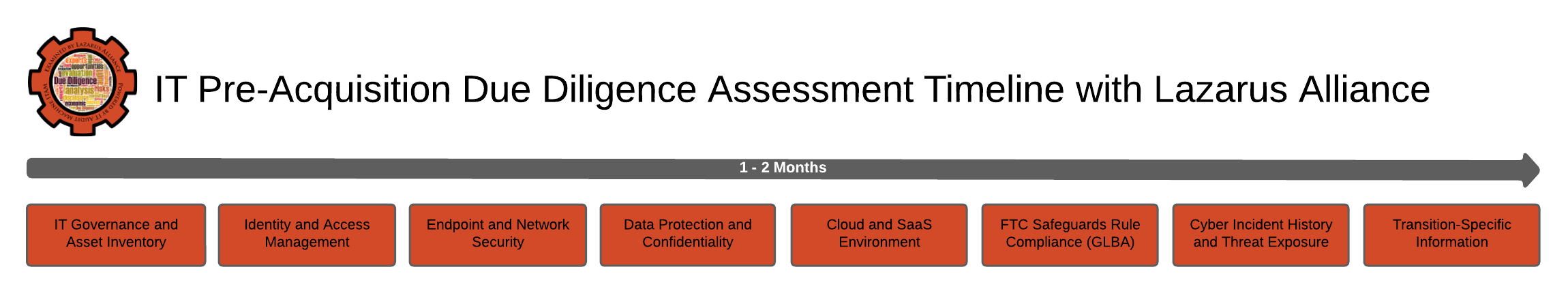
Typical Lazarus Alliance Audit Timeline
The CRL explicitly defines only the first milestone; the rest follows standard pre-acquisition due diligence logic (aligned with deal timing). Here is a realistic timeline based directly on the framework:
| Phase | Timing (from Kickoff) | Key Activities | Owner |
|---|---|---|---|
| Kickoff & CRL Issuance | Day 0 | Full Client Request List issued + Continuum GRC access | Lazarus Alliance and Deal Team |
| Wave 1 Collection | Days 1–14 | 18–20 highest-priority items (MSP contract, users, MFA, EDR, backups, etc.) | Target firm + MSP |
| Wave 1 Review & Wave 2 Issuance | Days 15–18 | Rapid review of Wave 1, red-flag identification, and tailored Wave 2 issued | Lazarus Alliance |
| Wave 2 Collection | Days 19–35 (≈2.5 weeks) | Remaining ~42 items (detailed policies, scans, SOC 2 reports, etc.) | Target firm + MSP |
| Full Analysis & Gap Assessment | Days 36–45 | Detailed risk mapping, FTC/GLBA review, and deal implications | Lazarus Alliance |
| Findings / Report Delivery | Days 46–56 (Week 7–8) | Final report delivered to the deal team | Lazarus Alliance and Deal Team |
Total typical duration: 4–8 weeks
- Fast-track (4–6 weeks): Possible with immediate MSP coordination and rapid Wave 2 turnaround.
- Standard (6–8 weeks): Recommended for most acquisitions to allow thorough review.
This compressed schedule front-loads the highest-risk items (still completed in the first two weeks) and keeps the entire engagement agile for tighter deal timelines. All documentation continues to be managed in the Continuum GRC portal.

Frequently Asked Questions
It is a structured, phased cybersecurity and IT due diligence review specifically designed for any organization undergoing M&A or private-equity transactions. Using a detailed Client Request List (CRL), it evaluates the target firm’s IT governance, security controls, data protection, regulatory compliance, and transition readiness across 8 key sections. The two-wave structure respects the operational capacity of a target organization. Wave 1 (18–20 items) delivers the highest-risk information within 14 days. Wave 2 (≈42 items) is issued only after Wave 1 review, so the scope can be adjusted based on findings, reducing unnecessary effort. The compressed timeline is 4–8 weeks from kickoff. Wave 1 is due in 14 days, Wave 2 collection takes ≈2.5 weeks, and the remaining time is used for analysis and final report delivery. Fast-track engagements can be completed in 4–6 weeks with strong MSP support. Simply upload a brief written confirmation (Word doc or email converted to PDF is fine). The absence of key documents is noted as an audit finding but is expected for many small firms and will not be penalized. Yes — we strongly recommend looping in your MSP at kickoff. Many Wave 1 exports (user accounts, MFA status, EDR coverage, patch reports) are most efficiently pulled directly from the MSP console. All documents, system exports, configuration records, and written confirmations are uploaded directly into the AI-powered Continuum GRC platform — Lazarus Alliance’s secure, enterprise-grade Governance, Risk, and Compliance system. Every submission is automatically protected with cryptographic hashing for immutable, tamper-proof evidence and a complete chain-of-custody. The platform’s intelligent evidence management engine automatically maps files to the corresponding audit steps, while built-in AI auditor tools perform real-time validation, gap detection, and compliance analysis. Progress is monitored through live dashboards with dynamic status tracking (NR, OS, PR, RC, NA, EX), automated alerts, and intelligent remediation recommendations — delivering a fully auditable, transparent, and highly efficient due diligence workflow. It provides immediate visibility into hidden risks, protects deal value through early identification of liabilities, ensures FTC Safeguards Rule / GLBA compliance, smooths post-acquisition transition, and gives the acquiring firm concrete data for valuation adjustments and remediation planning. Yes. Section F is dedicated to FTC Safeguards Rule (Gramm-Leach-Bliley Act) compliance, including the Written Information Security Program (WISP), Qualified Individual designation, risk assessment, training, and vendor oversight. A comprehensive final report with findings, risk ratings, gap analysis, prioritized recommendations, and transition considerations. The report is delivered to the deal team and can be used for negotiation, indemnification, or post-close remediation planning.
What is the Lazarus Alliance IT Pre-Acquisition Assessment?
Why is the assessment divided into Wave 1 and Wave 2?
How long does the full assessment take?
What if a requested document or policy does not exist?
Do we need to involve our Managed Service Provider (MSP)?
How are documents submitted and tracked?
What are the main benefits of this assessment?
Does the assessment cover regulatory compliance?
What deliverables will the acquiring firm receive?
Credentials You Can Count On
Lazarus Alliance is a proud member organization of the American Institute of Certified Public Accountants (AICPA), the Public Company Accounting Oversight Board (PCAOB), a peer review member of the Pennsylvania Institute of Certified Public Accountants (PICPA), and a member of the Delaware State Board of Accountancy licensed CPA firm: CF-0010876.
In addition, Lazarus Alliance holds the following prestigious accreditations as an Inspection Body, Inspection Laboratory, and Certification Body:
- American Association for Laboratory Accreditation (A2LA) ISO/IEC 17020 – Certification #3822.01
- American Accreditation Association (AAA) ISO/IEC 17021 – Certification #SC21202
- National Institute of Standards and Technology (NIST) ISO/IEC 17025 NVLAP Laboratory #600352-0
- American Association for Laboratory Accreditation (A2LA) ISO/IEC 17065 Laboratory
- Entidad Nacional de Acreditación (ENAC) ISO/IEC 17065 Laboratory

Talk with one of our experts
Our Lazarus Alliance Cybervisor™ teams have experience performing thousands of assessments for organizations providing services to clients around the world.

Benefits of a Lazarus Alliance IT Pre-Acquisition Assessment
The Lazarus Alliance IT Pre-Acquisition Assessment is purpose-built for M&A transactions across all industries. It delivers a fast, phased, low-disruption cybersecurity and IT due diligence process that gives the acquiring team immediate visibility into the target’s risk posture while respecting the operational realities of any size organization.
Proven across Finance, Healthcare, Technology, Manufacturing, Professional Services, and Private Equity portfolio companies.
Key benefits include:
- Front-Loaded Risk Visibility (Wave 1 in 14 Days): Delivers the 18–20 highest-risk items immediately.
- Respects the Target Company’s Capacity: Two-wave structure prevents overwhelming the target organization. Wave 2 is issued only after Wave 1 review and can be scoped based on findings.
- Comprehensive Coverage Across 8 Critical Sections: Spans IT governance, identity & access, endpoint/network security, data protection, cloud/SaaS posture, regulatory compliance, cyber incident history, and transition-specific risks. Focuses on the issues that most frequently create material findings or derail deals.
- Deal Protection & Value Preservation: Surfaces hidden liabilities before closing and provides concrete data for valuation adjustments, indemnification, or post-close remediation.
- Smooth Post-Acquisition Transition: Early visibility into system inventories, contract terms, credentials, and data-preservation obligations reduces migration surprises.
- Professional, Auditable Process: All documentation is managed in the secure Continuum GRC portal with standardized naming and status tracking.
- Regulatory & Compliance Assurance: Includes review of applicable regulations (FTC Safeguards Rule / GLBA, HIPAA, PCI DSS, ISO 27001, SOC 2, and others) relevant to the target’s industry.
Bottom line: This assessment compresses months of potential post-close surprises into a structured 4–8 week engagement. It protects the acquirer’s investment, de-risks the transaction, and works for companies in any industry.
Lazarus Alliance utilizes the Continuum GRC IT Audit Machine, Security Trifecta methodology, and Policy Machine to deliver internationally recognized “Best Practices” for establishing organizational security standards and controls. These support compliance with audit certifications and assessments.
