Lazarus Alliance SSAE 16 Assessment Services
From SSAE 16 Audits to IT Security Consulting, the experts at Lazarus Alliance provide a variety of services to fulfill your audit needs. SOC 1, SOC 2 and SOC 3: We are ready when you are!
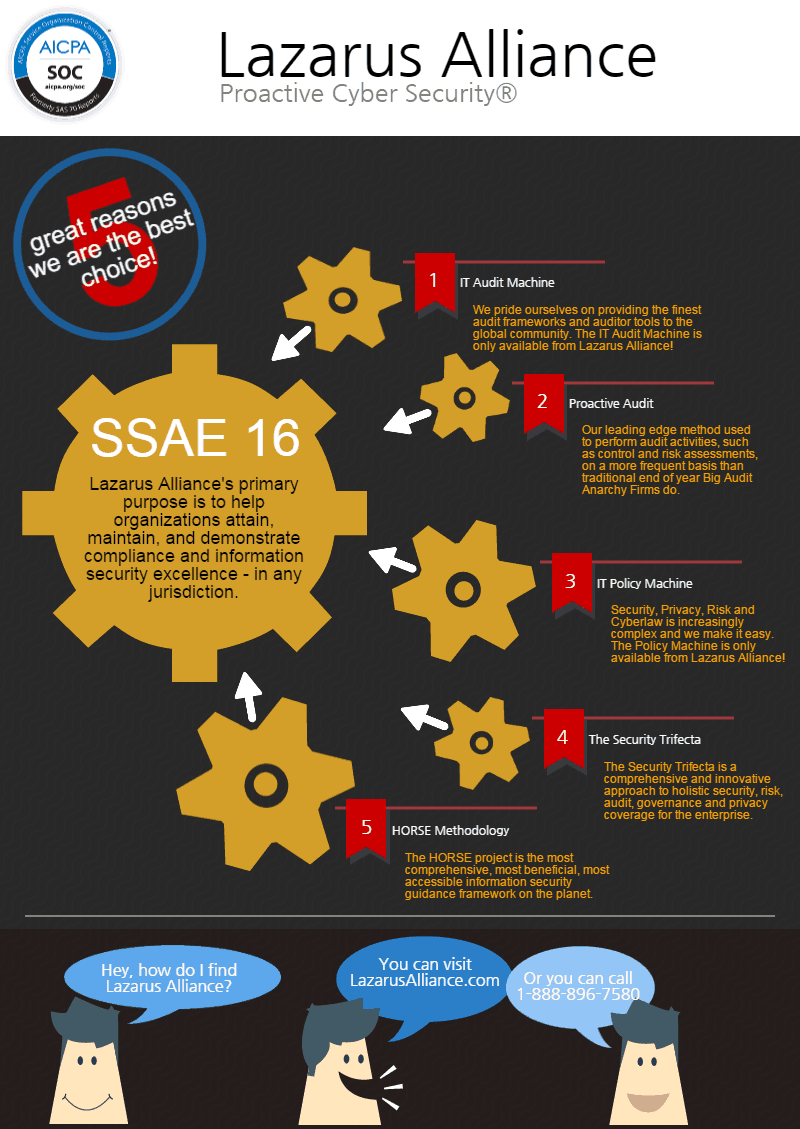
Lazarus Alliance is completely committed to you and your business success. Regardless of whether you represent the private sector or the public sector, we stand ready to partner with your organizations. Our competition may want to keep you and your employees in the dark where security, risk, privacy and governance are concerned hoping to conceal their methodology and expertise. We don’t prescribe to that philosophy. We believe the best approach is transparent and built on a partnership developed on trust and credibility creating sustainability within your organization.
Lazarus Alliance’s primary purpose is to help organizations attain, maintain, and demonstrate compliance and information security excellence – in any jurisdiction. Lazarus Alliance specializes in IT security, risk, privacy, governance,cyberspace law and compliance leadership solutions and is fully dedicated to global success in these disciplines.
Certifications Overview
SOC 1: Once a company has made the decision to enlist a third party to provide a service, they want assurances that those services will be provided timely, accurately, and securely. A SSAE 16 audit shows your commitment to maintaining a sound control environment that protects your client.s data and confidential information.
Not sure which report is right for your organization? Ask yourself these questions:
Will the report be used by your customers and their auditors to plan or perform an audit of their financial statements? If so, then the SOC 1 report is right for you.
SOC 2 and SOC 3: Service Organization Controls (SOC) 2 and 3 reports are designed to provide comfort over the following principles: Security, Confidentiality, Processing Integrity, Availability, and Privacy (if applicable) of a System in-scope. A System is holistically comprised of the Technology, People, Processes, and Data used to complete the services provided.
The following is a brief description of the goals to be achieved with each principle:
- Security: The system is protected against unauthorized access (both physical and logical).
- Confidentiality: Information designated as confidential is protected as committed or agreed.
- Processing Integrity: System processing is complete, accurate, timely, and authorized.
- Availability: The system is available for operation and use as committed or agreed.
- Online Privacy: Personal information obtained as a result of e-commerce is collected, used, disclosed, and retained as committed or agreed.
Still not sure which report is right for your organization? Ask yourself these questions:
Will the report be used by your customers or stakeholders to gain confidence and place trust in a service organization’s systems? If so, then the SOC 2 or SOC 3 report is right for you.
or
Do you need to make the report generally available or seal? If so, then the SOC 3 report is right for you.
We want to be your partner. For additional information please contact us!