IMPRESSUM STATEMENT
CONTACT AND REGULATORY INFORMATION
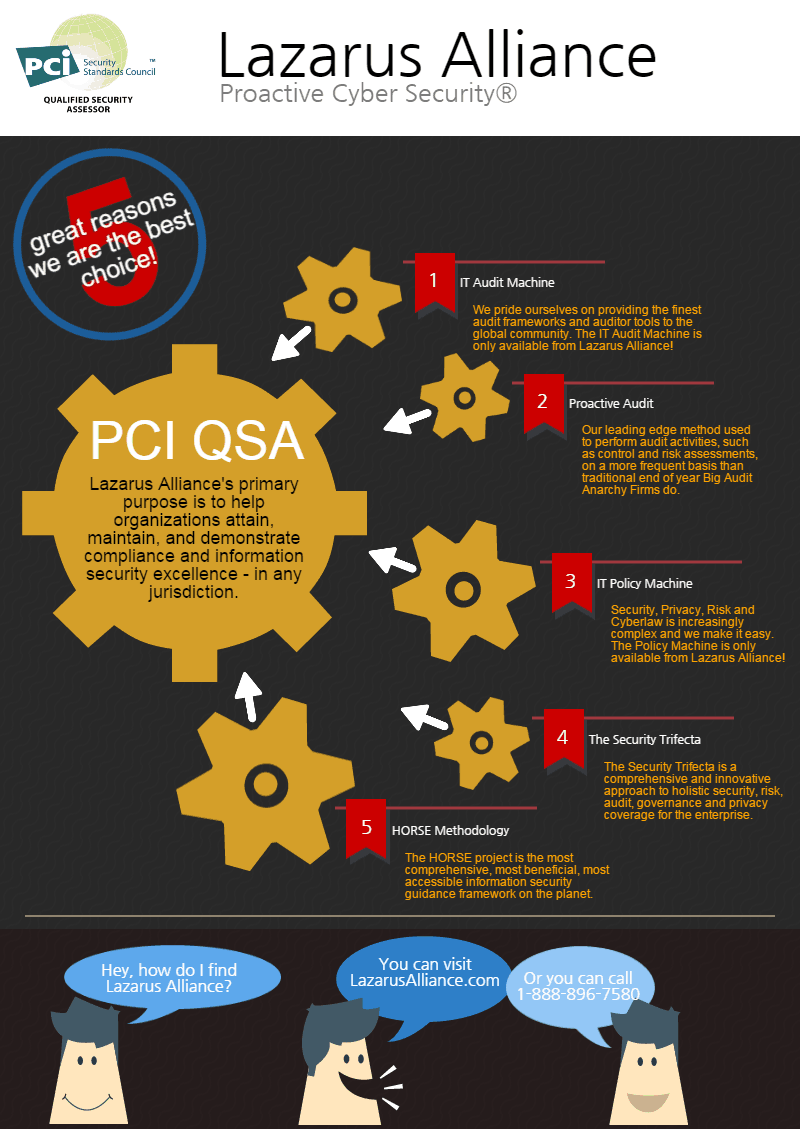
Impressum Statement: Founded in 2000, Lazarus Alliance has been passionately on the cutting edge of IT security, risk, privacy, governance, cyberspace law, and compliance leadership, innovation, and services provided to the global community. With significant contributions and innovations such as the IT Audit Machine, The Policy Machine, Cybervisor, ContinuumGRC, SafetyNET, the Holistic Operational Readiness Security Evaluation (HORSE Project), The The Security Trifecta, Your Personal CXO and other progressive initiatives helping companies eliminate nearly 96% of all cybersecurity risks, it’s no wonder that Lazarus Alliance has become a leading international name synonymous with incorruptible leadership, meaningful services, exceptional customer support and tangible innovations all specifically to prevent negative press and damage to your company, shareholders, employees and customers.
Lazarus Alliance’s primary purpose is to help organizations attain, maintain, and demonstrate compliance and information security excellence in any jurisdiction. Lazarus Alliance specializes in IT security, risk, privacy, governance, cyberspace law, and compliance leadership solutions and is fully dedicated to global success in these disciplines. Contact us and learn more about Lazarus Alliance and why Lazarus Alliance is Proactive Cybersecurity™!
Lazarus Alliance is a proud veteran-owned business.
Lazarus Alliance is a private stock corporation under United States law with headquarters in Phoenix, Arizona, United States.
Chairman of the Supervisory Board: Michael D. Peters
Chairman of the Board of Management: Michael D. Peters
Board of Management:
Michael D. Peters
Louise Candelaria
Lazarus Alliance, Inc.
27743 N. 70th Street,
Suite 100,
Scottsdale, AZ 85266
Phone: 1-888-896-7580
Email: legal@lazarusalliance.com
Internet: https://lazarusalliance.com