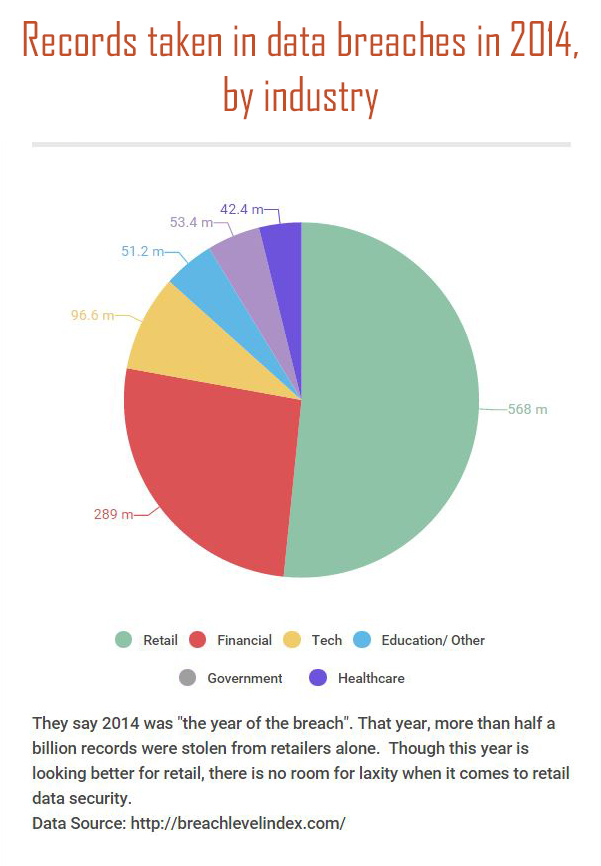
With the holiday season upon us, much attention turns to the retail sector, which is expected to see unprecedented activity as shoppers in a strengthening economy take advantage of seasonal deals and yet-further-expanded shopping hours. However, overshadowing the energy of the holiday shopping season, the specter of data breaches past sits more and more heavily on the minds of consumers and companies alike. As they whip out their credit cards and swipe their debit cards at millions of POS terminals this November, will the data on those cards be secure, or will they get their post-holiday statement to find mysterious charges and unfamiliar purchases?

The past few years have seen hundreds of data breaches of companies large and small. The ones that makes the headlines, of course, are the ones that involve millions and tens of millions of customers. But what can be done about the security of customer information? Where are the holes? And is there any hope of a victory over cyber criminals whose only job is to find ways around and through corporate security measures?
Well, according to cybersecurity experts, there is hope of at least holding our own, but only if organizations take serious strides to implement and vigilantly maintain stringent, systematic plans to ensure that not only their systems, but those of their partners and vendors are secure from data leaks. This requires that IT security teams be properly supported and funded and that security education and awareness be a part of company culture. It’s time, they stress, for the C-suite to make data security one of their primary concerns and, given the cost of data breaches and the frequency with which they are occurring, it would seem foolish to argue.
So let’s take a look at a few things we’ve learned from some of the biggest retail data breaches in the past few years.
Lesson 1: Vet your third-party vendors
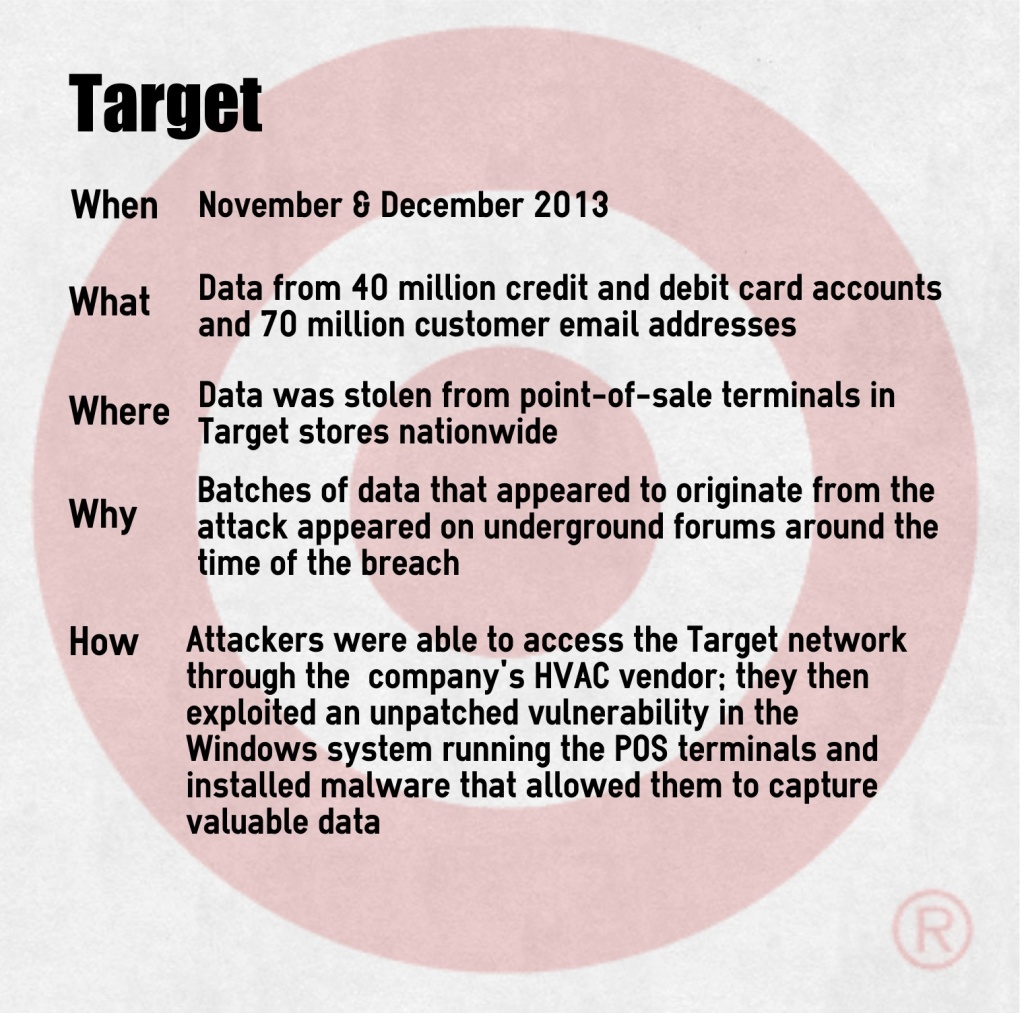
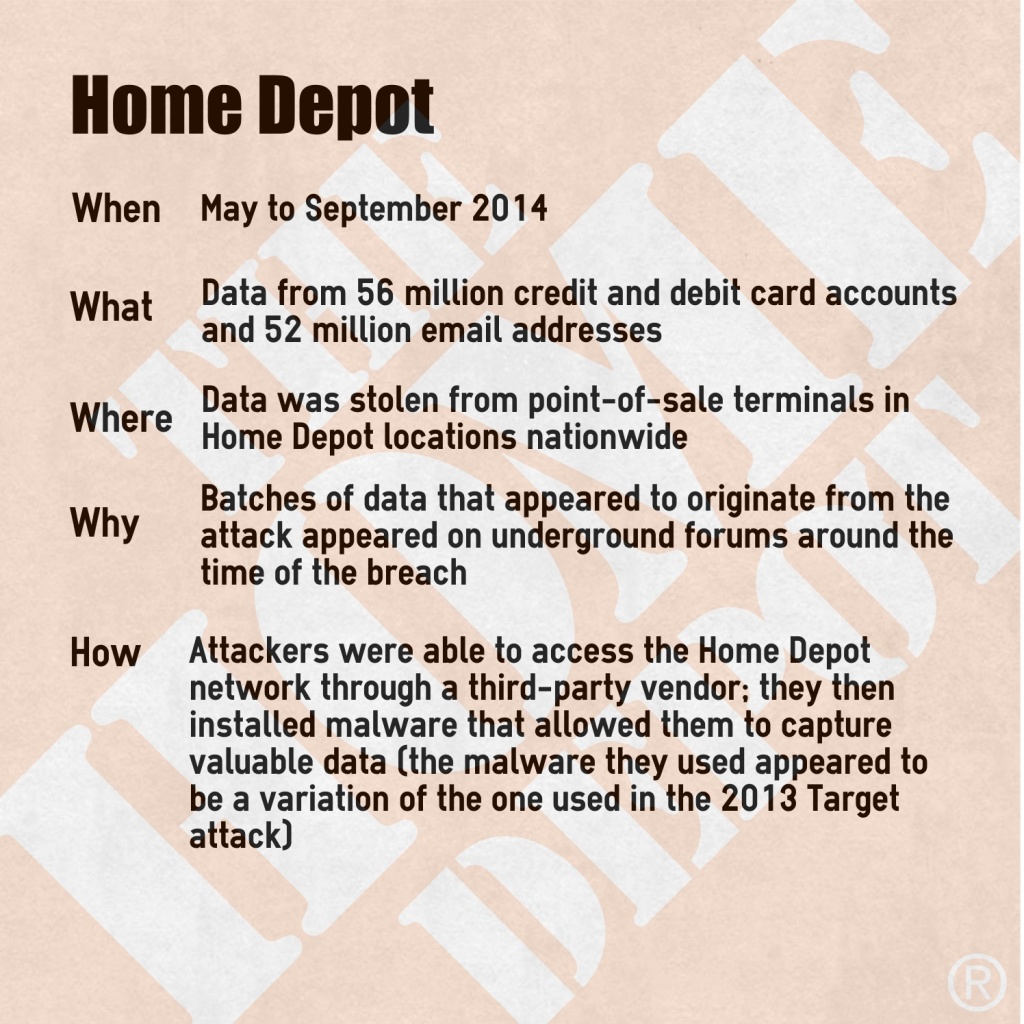
Target and Home Depot


More details
In both cases, investigations found evidence of the data’s being sold in batches on the “dark web” within a few weeks of being taken. The dark web consists in large part of a collection of forums and websites where criminals can buy and sell credit card information, personally identifiable information (PII), illicit substances, and any manner of illegal contraband. Banks and cybercrime experts monitor these forums watching for indications that their customers’ data have been compromised. It was bank security that raised the initial flag that led to the discovery of the Home Depot data breach.
A short time after the Home Depot data breach was reported,Brian Krebs, one of the foremost investigative reporters in the area of cybercrime, noted that the data from the latter data breach had appeared for sale on the same underground “shop” as the Target data had nearly a year earlier. Investigators, he said, had found that the Home Depot registers that had been attacked were infected with a variation of the same malware that had been used in the Target attacks. This software is designed to pull data from cards when they are swiped at an infected P.O.S. system.
So how did the malware get into the system in the first place? In both cases, the criminals gained access to the networks through the system of a third-party vendor. In Target’s case, it was the HVAC company that maintains their refrigerators – they had access to the Targets system so that they could monitor the units electronically. The Home Depot, too, indicated that the thieves got in “using credentials stolen from a third-party vendor”. Once in, they were able to exploit a vulnerability in Microsoft Windows, on which most POS systems run, to upload the malicious program.
What did we learn?
The practice of going after corporate data through vendors and subsidiaries is becoming more and more common. Where corporations can afford to spring for huge cybersecurity operations (though many have until now chosen not to), smaller vendors may struggle to keep on top of data security. There is, then, a lesson to be learned here for both big corporations and their third-party vendors. The lesson? Get it done. Organizations whose systems contain the personal and financial data of tens, sometimes hundreds of millions of customers have a responsibility to vet the vendors they work with (and the smaller companies they acquire) meticulously. Systems must be set up not only for ensuring security protocol is followed by any vendor given access to your system, but processes should be put in place so that they are able to access only what is absolutely necessary and to check that the security measures on their own systems are robust and reliable. Some things to look for, both in your own security protocol and in that of your vendors:
- Are the procedures in place for granting and removing systems access to employees satisfactory and are they being followed?
- Are security logs being routinely and consistently monitored to ensure that any attacks or data breaches are identified quickly?
- What kind of password security protocol is in place? Are employees required to change their passwords regularly? Are they well-educated on the importance of password security, the methods criminals use to acquire login and password information, and what constitutes a secure password? Does the company use two-factor authentication? (This last may not be a ‘must’, but it is certainly a good idea.)
- Are Bring-Your-Own-Device policies clear, comprehensive, and carefully enforced?
- Is the connection between your networks entirely secure? If sensitive data is being passed back and forth, do they have the capability to properly encrypt it?
- Is their network secure on a basic level? Do they have adequate firewalls, anti-virus, and anti-spam software? Are their terminals secure, or can anyone with a little motivation just walk in and access their system on-site? What do they do with decommissioned hardware?
- What is their patching policy? Do they have a process in place for ensuring that frequent patches from major software vendors like Microsoft are applied as soon as they are made available?
Highly regulated industries like financial services and insurance have long been advised – and in many instances required – to vet their third party vendors regularly and carefully. In the wake of recent data breaches, it seems clear that retail organizations would do well to follow the same advice.
Lesson 2: Data protection at all levels must be prioritized
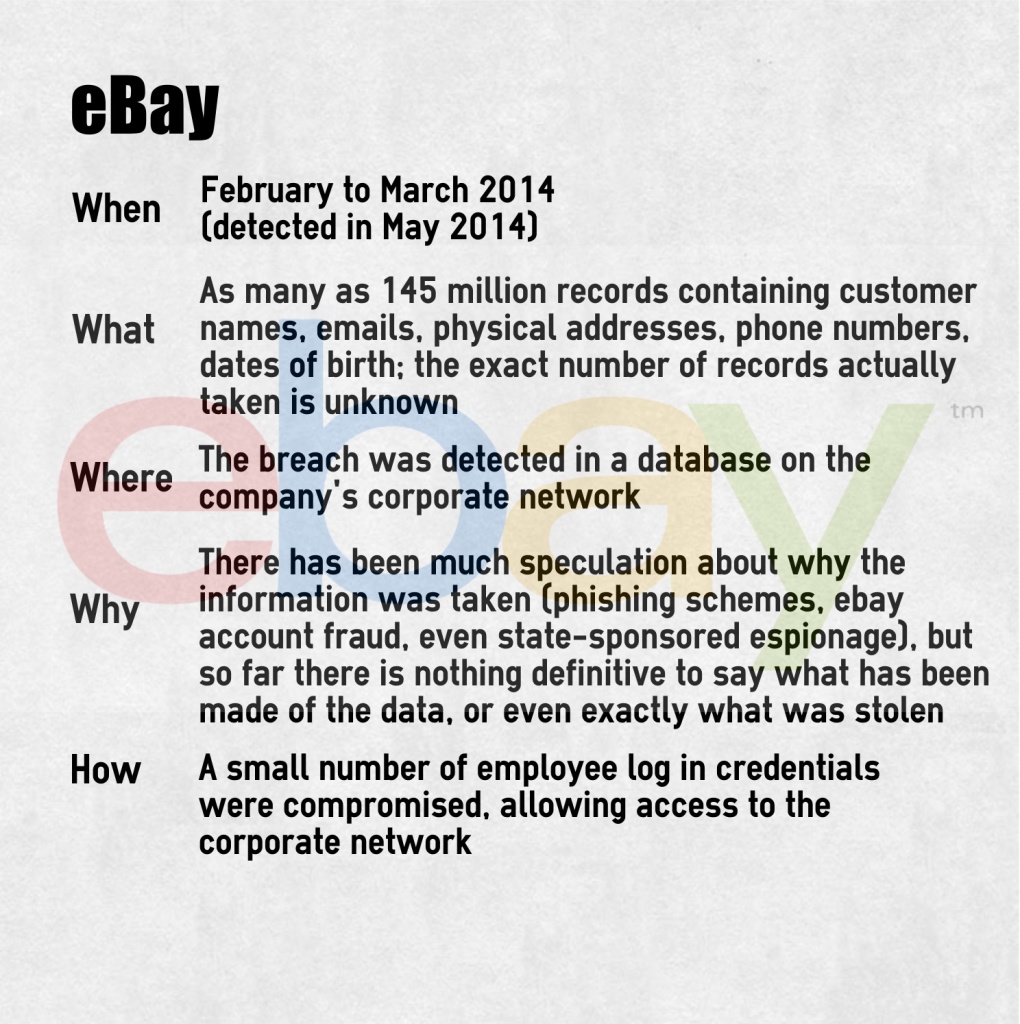
eBay
What did we learn?
In a report from the International Business Times following the attack, it was reported with regard to an investigation by the relevant regulatory bodies:
Of particular interest will be the lack of encryption used to protect customer names, email addresses, physical addresses, phone numbers and dates of birth. Investigators will also analyze why it took eBay nearly three months to detect the hackers, how long it took to fix the breach and how long the company waited to notify authorities and customers.
Knowing what went wrong in any situation helps to prevent making the same mistakes in the future. With the increase in identity theft and new account fraud, we now know that encrypting PII can be as important as encrypting financial information. We also know that data breaches can be difficult to detect if the right systems are not in place to make sure relevant data is reviewed by the right people in a timely manner. Just like any other business process, log reviews, protocol revisions, security updates need to be included in a company’s workflow. Not only can systems be set in place to ensure that every feasible measure is taken to protect sensitive information, but the right system can also enable an organization to integrate new protocols smoothly as new threats arise and new solutions are found. Given the pace at which cybercrime is advancing, it has now become imperative for companies to move plans for pervasive data security systems to the front burner, and to turn the temperature up to ‘high’.
Lesson 3: Everyone has to get involved in cybersecurity
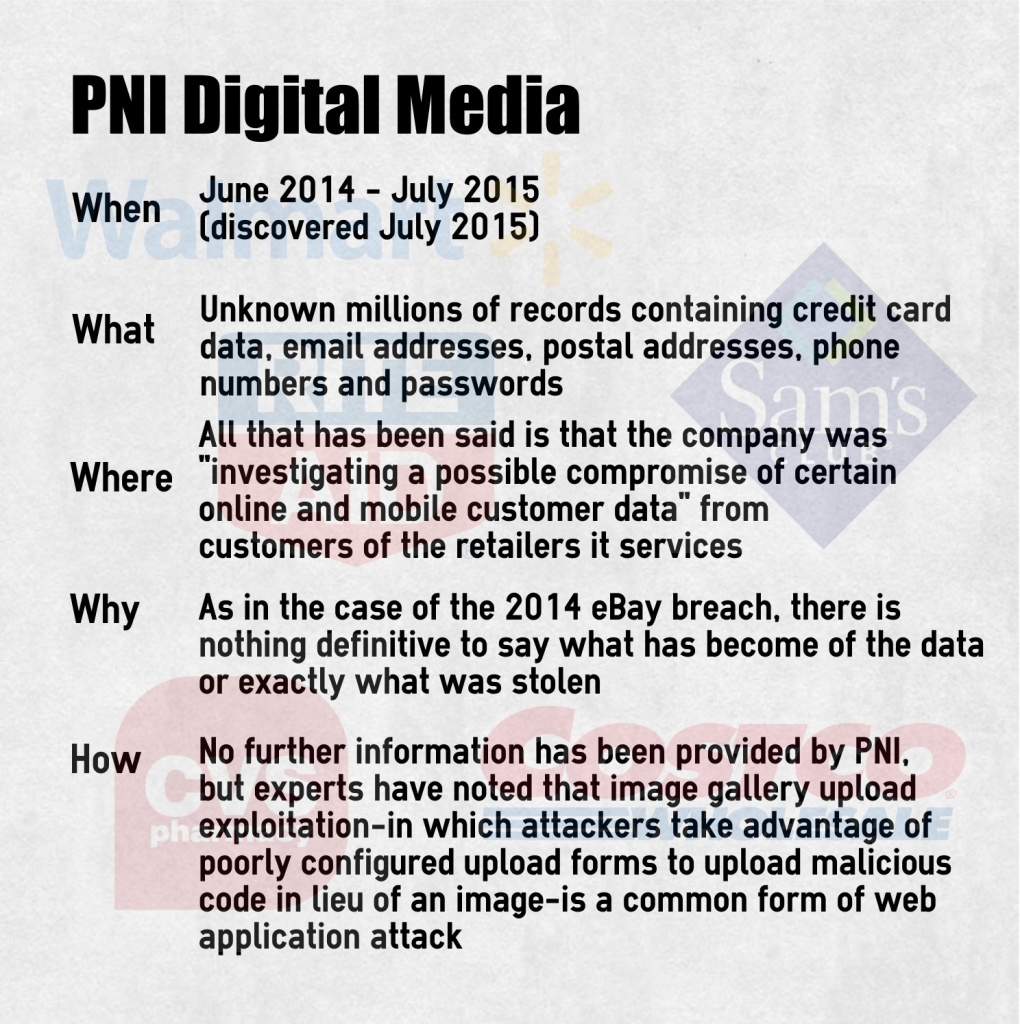
 PNI Digital Media
PNI Digital Media
(vendor for CVS, Sam’s Club, Costco, Rite Aid, Wal-Mart Canada, and others)
What did we learn?
With so little known about the PNI breach, there has been much speculation by experts as to how it happened, why it was allowed to happen, and why it went undetected for so long. While it may not be wise to give too much credence to speculation on a particular case, it can provide much insight into the overarching problems of retail data security and cybersecurity in general.
Boardroom support for Internet Security
When the news of the data breach first broke in July of this year, Brian Krebs noted that PNI Digital Media had been acquired by Staples Corporation around the same time that the PNI breach is thought to have first occurred, which seemed significant because Staples itself had suffered a breach that lasted some six months and exposed more than a million customer credit card records in mid-2014. While this may or may not stand as evidence that the company is giving inadequate attention to cybersecurity, it is the case that the importance of boardroom support for internet security efforts is at the forefront of security experts’ concerns.
This has been highlighted even more by the recent breach at Experian that exposed the personal information – including social security numbers – of 15 million T-mobile customers. During his investigations of that case, Krebs interviewed several security experts who had left the Experian security team because the company refused to dedicate adequate resources to securing the extremely sensitive information stored in the credit bureau’s digital files.
Following the massive breach at Target in 2013, similar concerns were raised as the company’s CIO resigned and a new CIO, CISO, and CCO were sought to take her place. Whether more leadership at the top is a solution to the problem remains to be seen, but the need for the C-suite to have a better understanding of and keep a more watchful eye on its digital security protocols is becoming clear.
Employee education
One of the most popular methods of infiltration for cybercriminals is through phishing. It is a very simple thing to find out who works for a given company and in what department. With a little social media skulking and seemingly-benign email contact, cybercriminals are able to obtain much of the information they need to access login and password information that can grant them broad access to corporate networks. In this day and age, employees must be well informed of the methods criminals use to obtain sensitive information. From clerical workers to the c-suite, everyone needs to understand basic preventative measures like how to recognize a phishing attempt and how to create and maintain secure passwords – and corporate policy needs to enforce for them the necessity of following security protocol.
Professional expertise from outside the company
Another recurring theme as companies seek to keep on top of cybercrime prevention is the question of whether data security is a task that should be left to the experts. Even for very large companies that are able to maintain security teams that can operate much like an independent security contractor might, the reality is that those teams often struggle to get the resources they need in an environment where their success may not be the top priority. In contrast, a security agency relies entirely on this strength to remain in business – they have no other task. External agencies are able to be objective about and prioritize security while drawing on a broad range of experience and deep well of expertise and knowledge. This is, in fact, one of the major benefits of moving to the cloud, presuming the right service provider is chosen. A reputable cloud host recognizes that the security of its servers and its ability to protect the data entrusted to it is pivotal to its continued existence. For this reason, cloud servers may well become some of the most secure places to store data into the future.
Government anti-cybercrime measures
Experts are divided on whether there is really much governments can do to stem the tide of cybercrime, which by its nature operates regardless of national borders. There are, though, many who believe governments will have to become involved, and soon, before the cost of cybercrime outstrips the benefits of conducting business in cyberspace. The call has been raised for an international governing body that would not only work to stop cyber criminals, but would regulate security measures so that companies around the world would be required to employ a strong baseline of prevention and detection methods.
Individual cyberhygiene
Finally, it is time for consumers to accept that they will have to step up their personal online protection if they are to keep their financial and personally identifiable information (PII) safe from criminals. Just as the time once came when folks began to lock their doors and keep the kids close to home, the time has now come to adopt certain precautions in the virtual world. This will mean that certain inconveniences like using a different password for every online service and storing those passwords in a secure app or, better, their own memories, must become a matter of habit. Credit card and loan offers that could once be discarded as junk mail now need to be shredded or otherwise disposed of securely and credit statements should be reviewed every month. Individuals must be diligent about not opening emails from unfamiliar addresses or clicking on unknown links. Even phone calls that seem to come from benign solicitors or even familiar institutions like banks and workplaces can be phishing attempts these days. The more consumers are educated about how to protect themselves from fraud and identify theft, the fewer claims a company has to cover and the less a store loses on fraudulent purchases that no one – not the credit card holder, the credit card company, or the credit card fraudster – is going to cover. What’s more, a customer who knows how to protect themselves will have greater confidence in the security of their information and a better informed consumer will always be a benefit to the market.
The time has come for everyone to recognize cybercrime as one of the major threats to economic security facing the individual and the corporation in today’s modern world. We may not yet know how to shut down cybercriminals completely, but there remains much to be done before we can say as a community that we have done all we can.
Cover image: “System Lock” by Yuri Samoilov, via Flickr, some rights reserved