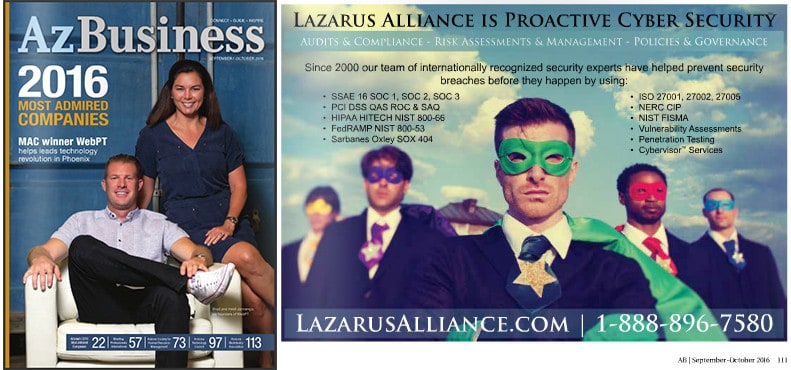
Even if you don’t have access to AZBusiness Magazine you can still check us out online. We are proud to be headquartered right here in Arizona and work with clients all around the world.
IoT Cyber Security Threatens Consumer Adoption of Smart Devices
If IoT cybersecurity concerns aren’t addressed, consumers will reject self-driving cars and other smart devices
Shortly after rideshare company Uber launched a pilot test of self-driving cars in Pittsburgh, competitor Lyft made the bold prediction that most of its cars would be self-driving within five years. While it can be argued that Lyft’s proclamation is overly optimistic, self-driving cars are no longer science fiction; rapid advances in machine learning and artificial intelligence are making it possible to turn more and more everyday gadgets and machines into smart Internet of Things (IoT) devices. However, consumers have grave concerns about the cybersecurity issues surrounding smart cars, smart thermostats, and other smart technology, and these concerns are not unfounded. Unless IoT manufacturers can ensure that IoT cybersecurity is solid, the IoT market could be severely hampered or, should a wide-scale hack occur, even grind to a halt.

Ransomware Possibly the Biggest Threat to IoT Cybersecurity
The IoT market is booming. Verizon predicts that the global market for IoT devices will grow from just under $600 billion in 2014 to $1.3 trillion in 2019. Although self-driving cars are still in their infancy, other smart devices, from fitness wearables to smart thermostats to connected insulin pumps, are ubiquitous. However, once a device connects to the internet, it immediately becomes a potential target for hackers, and IoT devices are particularly susceptible to ransomware attacks.
Recently, researchers at Intel Security discovered a vulnerability in a connected car that made it possible to install malware on the car’s infotainment system, causing the stereo to play the same song over and over. Many consumers are concerned about hackers being able to disable a smart car’s brakes or take control of its acceleration and steering. While these scenarios are possible, a ransomware attack on a smart car, which would render the car un-drivable until the owner paid a ransom, may be even more likely. Earlier this year, Hollywood Presbyterian Hospital paid a $17,000.00 Bitcoin ransom to hackers who had locked down the facility’s electronic health records. It’s reasonable to assume that a consumer who needs their car to get to work or drive their children to school may be willing to fork over several hundred dollars to a hacker, especially since trying to fix the car’s computer may cost that much or even more. If a hacker manages to disable a commercial fleet of self-driving vehicles, the affected company may be willing to pay that much per car.
The IoT cybersecurity threat extends to the smart home: Hackers could use ransomware to disable thermostats, security systems, even routers. Healthcare IoT cybersecurity is also a grave concern as pacemakers, insulin pumps, and other lifesaving devices are connected to the internet. Yet despite the gravity of the threats to connected devices, 90% of organizations have no cybersecurity plan to address IoT cybersecurity specifically, and 68% have no testing strategy for IoT devices.
Meanwhile, 58% of consumers report being “very concerned” or “highly concerned” about IoT cybersecurity. Smart device security isn’t just a cybersecurity issue; it’s a safety issue. If consumers do not feel that smart cars, smart thermostats, and other connected devices are safe, they will refuse to buy them or patronize businesses that use them. Manufacturers cannot afford to take a lackadaisical attitude toward IoT cybersecurity. Devices should be subjected to a comprehensive security evaluation and testing process before they are released into the marketplace, and businesses that purchase IoT devices should refuse to buy products that haven’t been proven safe.
The cybersecurity experts at Lazarus Alliance have deep knowledge of the cybersecurity field, are continually monitoring the latest information security threats, and are committed to protecting organizations of all sizes from security breaches. We offer full-service risk assessment services and Continuum GRC software to protect companies from data breaches, ransomware attacks, and other cyber threats.
Lazarus Alliance is proactive cybersecurity®. Call 1-888-896-7580 to discuss your organization’s cybersecurity needs and find out how we can help your organization secure your enterprise IoT devices.
Lazarus Alliance Receives Accreditation as FedRAMP 3PAO
IT Cybersecurity and GRC firm becomes authorized to validate Cloud Service Providers to new FedRAMP standards
Phoenix, Arizona, September 12, 2016 (Newswire.com) – Today, Lazarus Alliance Inc. announced that it has achieved accreditation as a FedRAMP (Federal Risk and Authorization Management Program) Third Party Assessment Organization (3PAO).
The FedRAMP program supports the U.S. government’s objective to enable U.S. federal agencies to use managed service providers that enable cloud computing capabilities, and Lazarus Alliance is one of the few accredited 3PAO firms in the world with this designation. With this certification, Lazarus Alliance is the only assessment firm authorized to conduct assessments for the federal government (3PAO), the Health-care industry (HIPAA, HITECH, Meaningful Use, NIST 800-66), the Payment Card Industry (Qualified Security Assessor), the Service Provider industry ((SSAE 16 (SOC 1), AT 101 (SOC 2), SysTrust / WebTrust (SOC 3)), NERC CIP, the Public sector (SOX 404), and advisors in ISO 27001, 27002, 27005 using the formidable combination of the IT Audit Machine (ITAM) and our Cybervisors.
FedRAMP provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services. As a part of the FedRAMP process, cloud service providers (CSPs) must use a FedRAMP approved third party assessor to independently validate and verify that they meet the FedRAMP requirements.
“Even taking a pragmatic approach, the cloud raises a plethora of cybersecurity concerns for any business,” said Michael Peters, CEO at Lazarus Alliance. “For government agencies, these concerns can be even more sensitive since national security can be at risk and as the largest employer in the world, it goes way beyond that. The 3PAO accreditation further confirms Lazarus Alliance’s expertise in cloud cybersecurity, risk assessments and we look forward to working with CSPs around the world on their FedRAMP initiatives toward receiving an authority to operate (ATO).”
Lazarus Alliance is one of the very few organizations worldwide to obtain this classification as an inspection body to assess cloud systems for the federal government. FedRAMP is the first United States government-wide program that provides a standardized approach to security assessment, authorization and continuous monitoring for cloud-based services. In order to receive accreditation, Lazarus Alliance demonstrated an advanced level of technical proficiency and compliance experience. According to the A2LA, the “assessment process involves a rigorous evaluation of technical competence of the 3PAOs as well as an assessment of their compliance with international standards.”
Receiving the accreditation of 3PAO means Lazarus Alliance will be able to validate the security and control implementations that CSPs must provide in order to work with and provide cloud services to federal agencies. 3PAOs are critical to the FedRAMP program, as they demonstrate the independence and competency of CSPs that host the government’s most crucial data.
In addition to demonstrating the requisite technical competency in FISMA and independence and quality management to achieve 3PAO accreditation, Lazarus Alliance has diverse leadership experience in additional vital audit & compliance fields, risk assessment & management, and governance & policies. Lazarus Alliance staff members are heavily experienced in those respective industry regulations and are located across the United States.
Inquiries for FedRAMP services can be made with Lazarus Alliance at 877-896-7580 or at https://lazarusalliance.com/services/audit-compliance/fedramp/
[wp-booklet id=1442]
About Lazarus Alliance
Lazarus Alliance is a leading, independent information technology Security, Governance, Risk and Compliance (IT GRC) firm that provides IT Audit & Compliance, Risk Assessment & Management, Governance & Policies, and Cybervisor supported solutions. Founded in 2000, Lazarus Alliance is a proud veteran owned business and has been passionately on the cutting edge of IT security, risk, privacy, governance, cyberspace law and compliance leadership, innovation and services provided to the global community. With significant contributions and innovations such as the IT Audit Machine, The Policy Machine, Cybervisor, Continuum GRC, SafetyNET, the Holistic Operational Readiness Security Evaluation (HORSE Project)®, the Security Trifecta, Your Personal CXO, and other progressive initiatives, it’s no wonder that Lazarus Alliance has become a leading international name synonymous with incorruptible leadership, meaningful services, exceptional customer support and tangible innovations all specifically to prevent negative press and damage to our client’s companies, their shareholders, employees and customers. Lazarus Alliance’s primary purpose is to help organizations attain, maintain, and demonstrate compliance and information security excellence, in any jurisdiction. Contact us and learn more about Lazarus Alliance and why Lazarus Alliance is Proactive Cybersecurity.