Lazarus Alliance: Proactive NIST CSF & 800-53 Audit Services. Call +1 (888) 896-7580 today!
Table of Contents
Toggle

Lazarus Alliance’s pre-assessment process provides organizations with a targeted, efficient review of their NIST CSF 2.0 program by directly examining the underlying NIST SP 800-53 control implementations through rigorous validation testing. As an A2LA-accredited laboratory and certified 3PAO, Lazarus Alliance leverages its Security Control Assessment & Validation (SCA-V) services and proprietary Continuum GRC IT Audit Machine™ (ITAM) platform to bridge the high-level, outcome-based CSF (106 Subcategories) with the detailed, prescriptive controls in NIST 800-53 Rev. 5.
NIST CSF organizes its Core into 6 high-level Functions and 22 Categories (the Categories sit under the Functions and contain the 106 Subcategories).
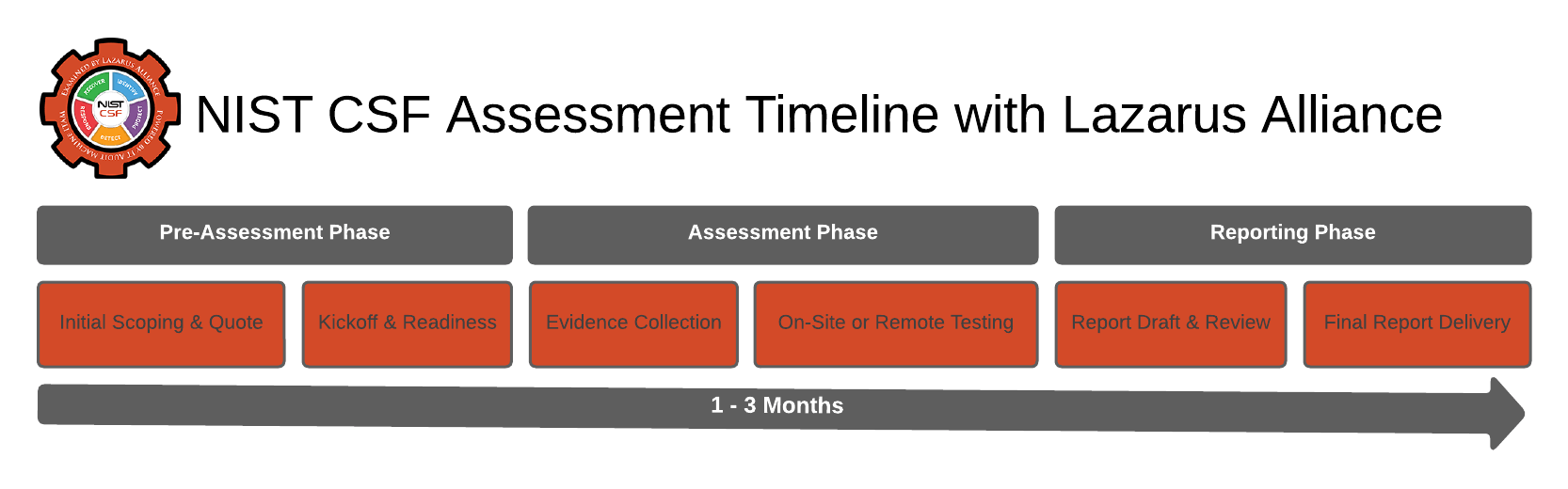
Lazarus Alliance, a certified Third-Party Assessment Organization (3PAO), will collaborate directly with your organization to schedule your NIST CSF & 800-53 assessment. Our certified 3PAO assessors will assist in determining the appropriate impact level based on your company’s unique business and government requirements.
The following matrix represents the required functions to achieve CSF compliance.
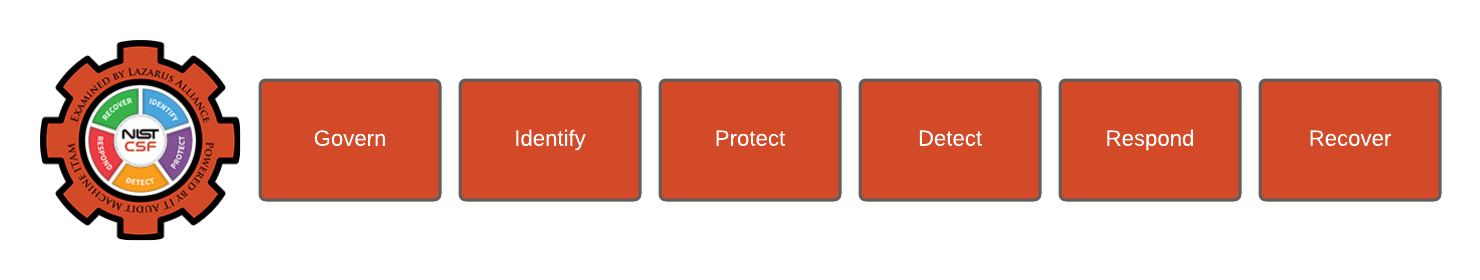
- Govern (GV): The organization’s cybersecurity risk management strategy, expectations, and policy are established, communicated, and monitored.
- Identify (ID): The organization’s current cybersecurity risks are understood.
- Protect (PR): Safeguards to manage the organization’s cybersecurity risks are used.
- Detect (DE): Possible cybersecurity attacks and compromises are found and analyzed.
- Respond (RS): Actions regarding a detected cybersecurity incident are taken.
- Recover (RC): Assets and operations affected by a cybersecurity incident are restored.
The following matrix represents the required functions to achieve 800-53 compliance.
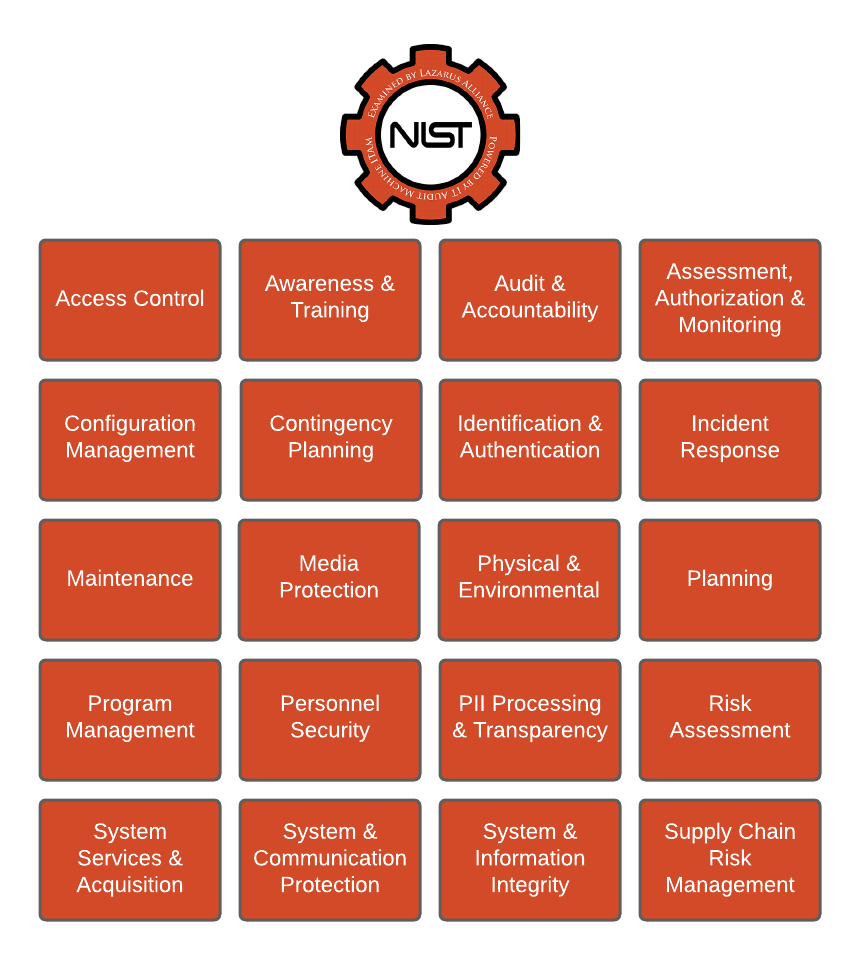
A System is holistically comprised of the Technology, People, Processes, and Data used to complete the services provided. The 800-53 certification is designed to provide comfort over the following principles described in brief:
- Access Control: This control environment measures the security features of the system boundary that control access rights and resources. Areas to be examined include, but are not limited to: account management, access enforcement, unsuccessful login attempts, system use notification, permitted actions, permitted actions without identification/authorization, remote access, wireless access, access control for mobile devices, use of external information systems, and publicly accessible content.
- Awareness and Training: This control environment measures the security awareness training that the organization has in place, with respect to the system boundary. Areas to be examined include, but are not limited to: security awareness, security training, and security training records.
- Audit and Accountability: This control environment measures the resources in place to measure and hold accountable audit practices over the system boundary. Areas to be examined include, but are not limited to: audit events, content of audit records, audit storage and capacity, response to audit processing failures, audit review process, time stamps, and protection of audit information, audit record retention, and audit generation.
- Assessment Authorization and Monitoring: This control environment examines how organizations assess controls in systems and the environments in which those systems operate as part of initial and ongoing authorizations, continuous monitoring, FISMA annual assessments, system design and development, systems security engineering, privacy engineering, and the system development life cycle.
- Configuration Management: This control environment examines the configurations around the system boundary. Areas to be examined include, but are not limited to: baseline configurations, security impact analysis, configuration settings, least functionality, information system component inventory, software usage restrictions, and user-installed software.
- Contingency Planning: This control environment examines the organization's processes around contingencies. Areas to be examined include, but are not limited to: the contingency plan, contingency training, plan testing, information system backup, and information system recovery and reconstitution.
- Identification and Authentication: This control area examines the procedures and tools in place to identify and authenticate users who are granted access to the system boundary. Areas to be examined include, but are not limited to: identification and authentication, identifier management, authenticator management, authenticator feedback, and cryptographic module authentication.
- Incident Response: This control area examines the process and practices in place for handling and responding to incidents within the system boundary. Areas to be examined include, but are not limited to: incident response training, handling, monitoring, reporting, response assistance, and the incident response plan.
- Maintenance: This control area examines the processes and procedures in place that support controlled maintenance within the system boundary. Areas to be examined include, but are not limited to: controlled maintenance, nonlocal maintenance, and maintenance personnel.
- Media Protection: This control area examines the processes and procedures in place that support proper protections around system media assets. Areas to be examined include, but are not limited to: media access, sanitization, and disposal.
- Physical and Environmental: This control area examines the process and procedures in place, which support proper physical and environmental protections to the system boundary. Areas to be examined include, but are not limited to: physical access control and authorizations, monitoring physical access, visitor access records, emergency lighting, fire protection, temperature and humidity controls, water damage protection, and delivery and removal.
- Planning: This control area examines the processes in place around proper planning for the system boundary. Areas to be examined include, but are not limited to: The System Security Plan and rules of behavior.
- Program Management: This control environment measures the organization’s status in the development and implementation of an organization-wide information security program to address information security for the information and information systems that support the operations and assets of the organization, including those provided or managed by another organization, contractor, or other source.
- Personnel Security: This control environment measures the practices and processes in place that examine, screen, and review personnel assigned to the system boundary. Areas to be examined include, but are not limited to: position risk designation; personnel screening, termination, and transfer; access agreements, third-party personnel, and personnel sanctions.
- Personally Identifiable Information Processing and Transparency: This control environment measures the Personally Identifiable Information; Any representation of information that permits the identity of an individual to whom the information applies to be reasonably inferred by either direct or indirect means.
- Risk Assessment: This control area examines the process and procedures in place, which measure risk and vulnerabilities to the system boundary. Areas to be examined include, but are not limited to: security categorization, risk assessment, and vulnerability scanning.
- System Services and Acquisition: This control environment measures the practices and processes in place for the development of the system boundary. Areas to be examined include, but are not limited to: allocation of resources, the system development life cycle, acquisition process, information system documentation, and external information system services.
- System and Communication Protection: This control area examines the process and procedures in place, which measure the protection of the system boundary. Areas to be examined include, but are not limited to, denial of service protection, boundary protection, cryptographic key establishment, protection and management, collaborative computing devices, secure name/address resolution devices, provisioning architecture, and process isolation.
- System and Information Integrity: This control environment measures the practices and processes in place for the assurance of system boundary integrity. Areas to be examined include, but are not limited to: flaw remediation, malicious code protection, information system monitoring, and information handling and retention.
- Supply Chain Risk Management: This control environment measures the practices and processes in place for identifying, assessing, and mitigating ICT supply chain risks at all levels of their organizations.
Lazarus Alliance 800-53 client services will schedule our team to prioritize this engagement based on the needs of the client and ensure a timely delivery of the required compliance package, subject to client resources being available.
Frequently Asked Questions
What is FISMA and why is it important for federal agencies and contractors?
FISMA (Federal Information Security Modernization Act) is a U.S. law that mandates federal agencies and their contractors to develop, document, and implement an information security program to protect federal information systems. It ensures consistent security practices, risk management, and accountability, helping organizations avoid penalties, maintain contract eligibility, and safeguard sensitive data from threats like cyberattacks.
What is NIST 800-53, and how does it relate to FISMA audits?
NIST Special Publication 800-53 is a comprehensive catalog of security and privacy controls organized into 20 families (e.g., Access Control, Incident Response, Risk Assessment). It provides guidelines for protecting information systems against threats and ensuring compliance with laws like FISMA. In federal contexts, there is no separate "NIST 800-53 audit"—it's integrated into FISMA audits as the core evaluation framework, using controls tailored to the system's impact level (Low, Moderate, or High).
Who is the target audience for Lazarus Alliance’s FISMA/NIST audit services?
These services are primarily for U.S. federal agencies and contractors handling federal data, where compliance is mandatory. They're also ideal for private organizations in sectors like critical infrastructure, healthcare, finance, or those pursuing federal contracts, FedRAMP authorization, or robust cybersecurity—regardless of system type (cloud, on-premises, or hybrid).
| Impact Level | Baseline Controls (Approx.) | Key Use Cases | Reuse Scope |
|---|---|---|---|
| Low | ~125 NIST 800-53 Low controls | Public/low-sensitivity data (e.g., general websites) | SLED entities nationwide |
| Low+ | Enhanced Low (~150 controls) | Slightly elevated low-risk data (e.g., basic admin tools) | SLED entities nationwide |
| Moderate | ~325 NIST 800-53 Moderate controls + overlays | Confidential data (e.g., PII, financial records) | SLED entities nationwide |
| High | ~421 NIST 800-53 High controls + overlays | High-sensitivity data (e.g., critical infrastructure) | SLED entities nationwide |
| Core (Introduced May 2025) | 60 foundational Moderate controls (MITRE ATT&CK mapped) | Entry-level validation for progressing products | Broad pre-authorization access for SLED |
- Comprehensive Cybervisor™ Assessments using advanced software for low, moderate, and high-impact baselines.
- Ongoing proactive monitoring and 24/7 audit platform access.
What is the audit process with Lazarus Alliance?
As a certified Third-Party Assessment Organization (3PAO), Lazarus Alliance schedules assessments directly with your team, determines the appropriate system impact level based on FIPS 199 and your business needs, and evaluates controls using NIST 800-53. The process incorporates tools like the Security Trifecta methodology and Continuum GRC for tailored, risk-based assessments, leading to Authorization to Operate (ATO) recommendations and continuous monitoring support.
What are the key benefits of achieving NIST 800-53 and FISMA compliance?
Compliance strengthens your security posture against threats, ensures alignment with regulations like FedRAMP, HIPAA, and GDPR, and adopts a scalable, risk-based approach. It builds trust with stakeholders, reduces breach costs through proactive controls, enhances incident response, protects privacy (e.g., via data minimization for PII), and supports long-term efficiency and interoperability for federal or commercial operations.
How does Lazarus Alliance stand out as a FISMA/NIST audit provider?
Lazarus Alliance is an A2LA-accredited 3PAO (ISO/IEC 17020 certification #3822.01) with global experience conducting thousands of assessments via Cybervisor™ teams. They offer customized evaluations integrated with the NIST Risk Management Framework (800-37), proprietary tools for automated control mapping, and a focus on multi-regulatory compliance—ensuring efficient, high-quality results without separate NIST-only audits.
Can non-federal organizations benefit from NIST 800-53 audits?
Yes, while mandatory for federal entities, NIST 800-53 is widely adopted by private sector organizations for voluntary cybersecurity enhancements. It provides a flexible framework for protecting systems, meeting industry standards, and preparing for contracts or audits in regulated environments, making it valuable for any business prioritizing data security and privacy.
What role does privacy play in NIST 800-53 controls?
NIST 800-53 includes dedicated privacy controls (e.g., in the Privacy family) alongside security ones, emphasizing principles like data minimization, transparency, and consent for handling personally identifiable information (PII). This integration supports compliance with privacy laws like CCPA or GDPR, ensuring balanced protection of both security and individual rights in federal and commercial systems.

Benefits of NIST 800-53 Compliance
NIST 800-53 compliance offers numerous benefits for organizations, particularly those handling federal data, but also for private entities adopting the framework. Below is a concise list of key benefits:
- Enhanced Security Posture:
- Implements robust security and privacy controls to protect systems and data from threats like cyberattacks, data breaches, and insider threats.
- Addresses modern risks, including supply chain vulnerabilities and advanced persistent threats.
- Regulatory Compliance:
- Risk-Based Approach:
- Tailors controls to the organization’s specific risk profile and system impact level (Low, Moderate, High), optimizing resource allocation.
- Promotes proactive risk management through continuous monitoring and assessment.
- Improved Trust and Credibility:
- Demonstrates commitment to security and privacy, building confidence among customers, partners, and stakeholders.
- Enhances reputation, especially for contractors seeking federal business or organizations in regulated industries like healthcare or finance.
- Interoperability and Consistency:
- Provides a standardized framework, ensuring consistent security practices across systems, vendors, and partners.
- Facilitates integration with other frameworks like the NIST Cybersecurity Framework or ISO 27001.
- Privacy Protection:
- Incorporates privacy controls (e.g., data minimization, transparency) to safeguard personally identifiable information (PII), aligning with regulations like GDPR or CCPA.
- Reduces legal and reputational risks associated with privacy violations.
- Scalability and Flexibility:
- Adaptable to various system types (cloud, on-premises, hybrid) and organization sizes, from small businesses to large enterprises.
- Allows tailoring of controls to meet specific operational needs without compromising security.
- Incident Preparedness and Response:
- Strengthens incident detection, response, and recovery capabilities through controls like Incident Response (IR) and System Monitoring (SI).
- Minimizes downtime and financial losses from security incidents.
- Cost Efficiency in the Long Term:
- Prevents costly breaches and remediation by proactively addressing vulnerabilities.
- Streamlines compliance efforts by providing a unified framework, reducing redundant processes for multiple regulations.
- Support for Authorization to Operate (ATO):
- Facilitates obtaining and maintaining ATO for federal systems by demonstrating compliance with NIST 800-53 controls, critical for federal contracts or cloud service providers under FedRAMP.
Context-Specific Benefit
For organizations working with a 3PAO like Lazarus Alliance, NIST 800-53 compliance ensures a structured assessment process to identify the correct impact level and implement tailored controls, streamlining FISMA audits and enhancing federal contract readiness.
By adopting NIST 800-53, organizations not only meet regulatory requirements but also build a resilient, trustworthy, and efficient security framework.

Talk with one of our experts
Our Lazarus Alliance Cybervisor™ teams have experience performing thousands of assessments for organizations providing services to clients around the world.
We're here to answer any questions you may have.

Credentials You Can Count On

American Association for Laboratory Accreditation (A2LA) ISO/IEC 17020 accredited certification number 3822.01.
Lazarus Alliance utilizes the Continuum GRC IT Audit Machine, Security Trifecta methodology, and Policy Machine to deliver internationally recognized “Best Practices” for establishing organizational security standards and controls. These support compliance with NIST 800-53-based audit certifications and assessments.